Improved Biba model based on trusted computing - Liu - 2015 - Security and Communication Networks - Wiley Online Library
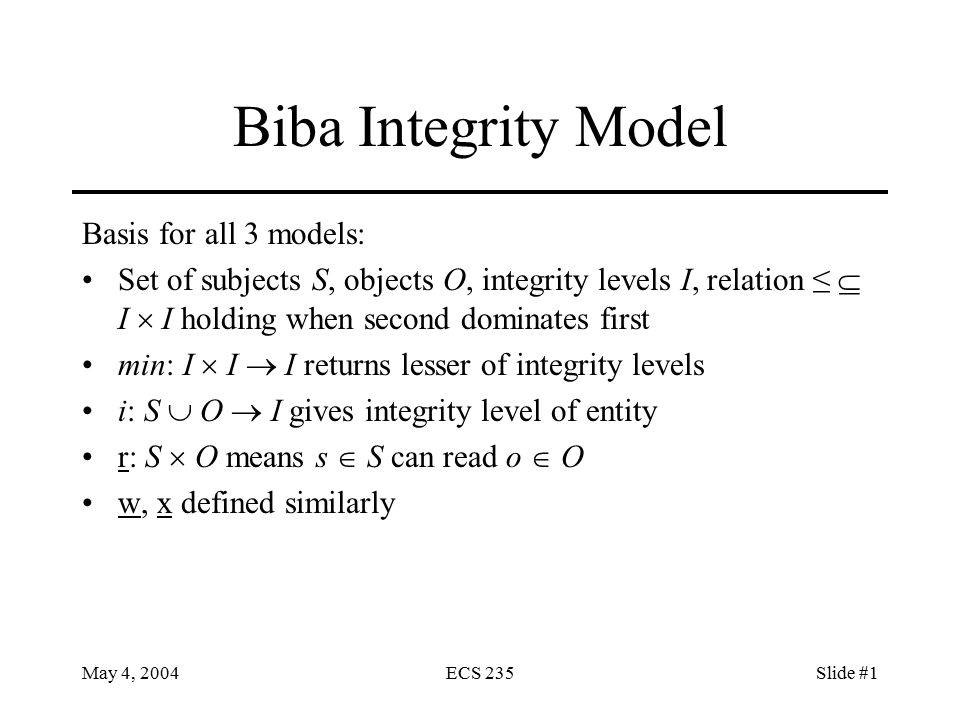
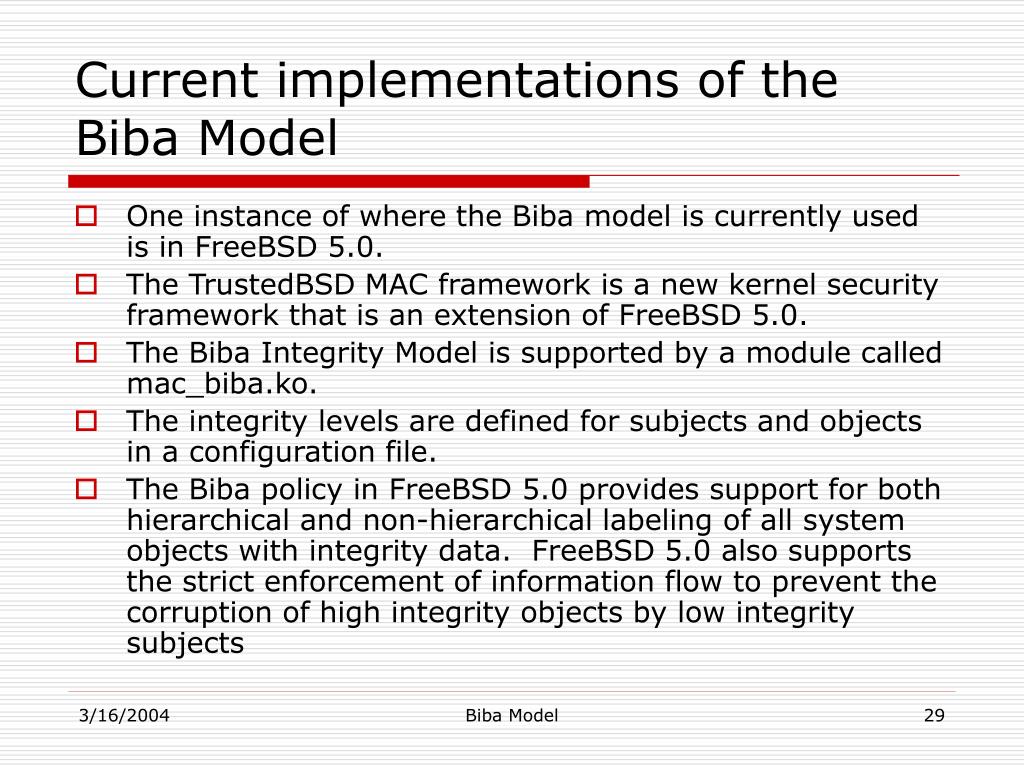
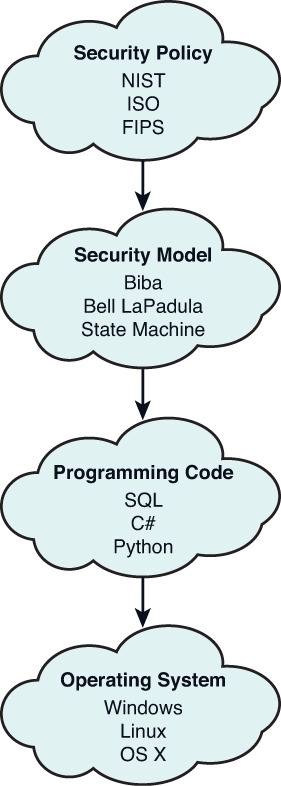
May 4, 2004ECS 235Slide #1 Biba Integrity Model Basis for all 3 models: Set of subjects S, objects O, integrity levels I, relation ≤ I I holding when. - ppt download
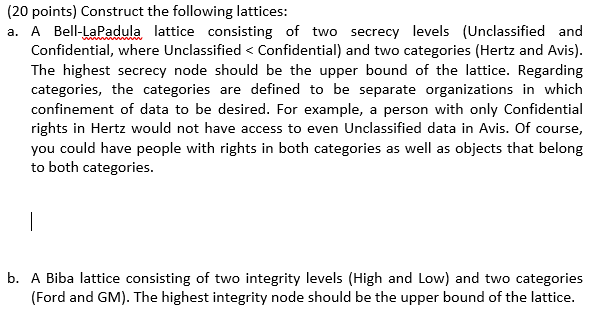
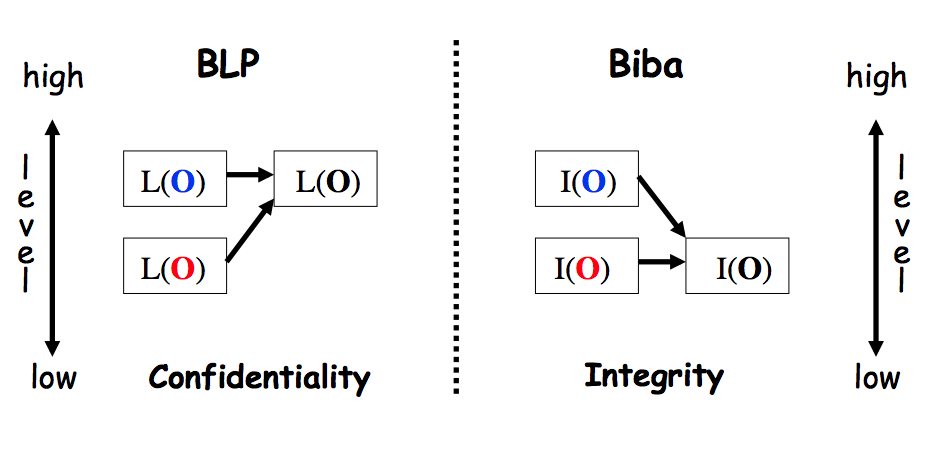
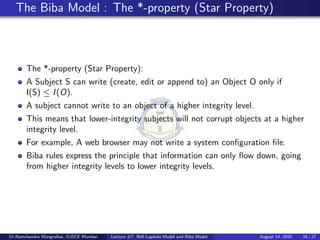
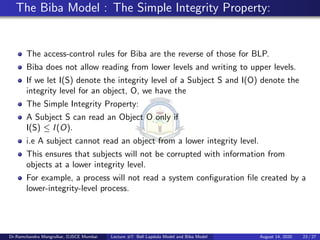
Outline Bell-LaPadula, linear case High watermark property Biba and low watermark Information-flow perspective