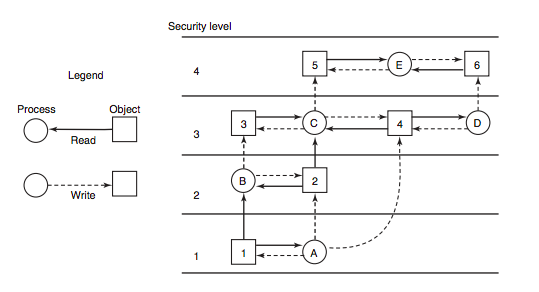
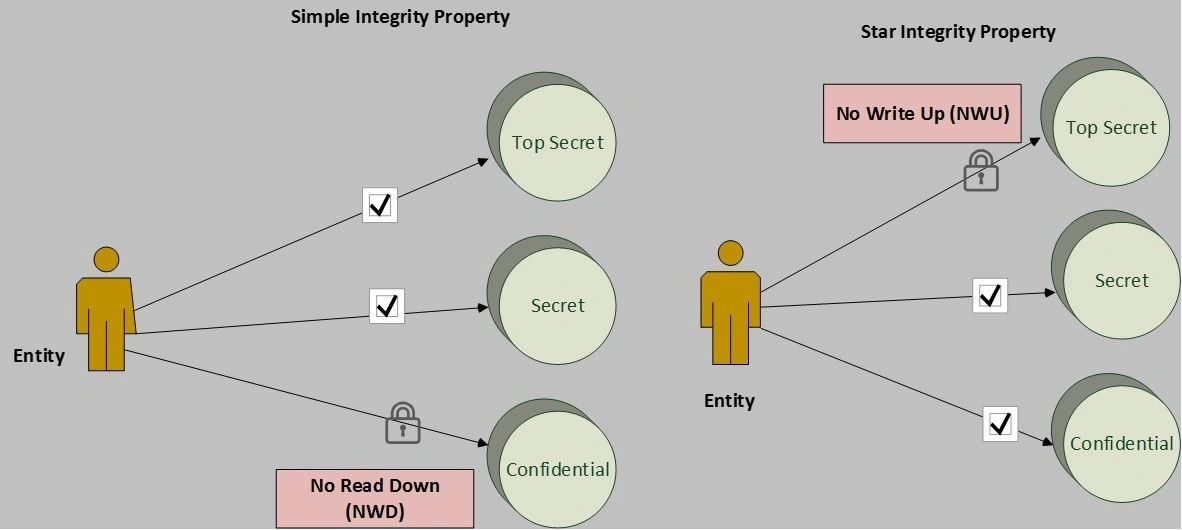
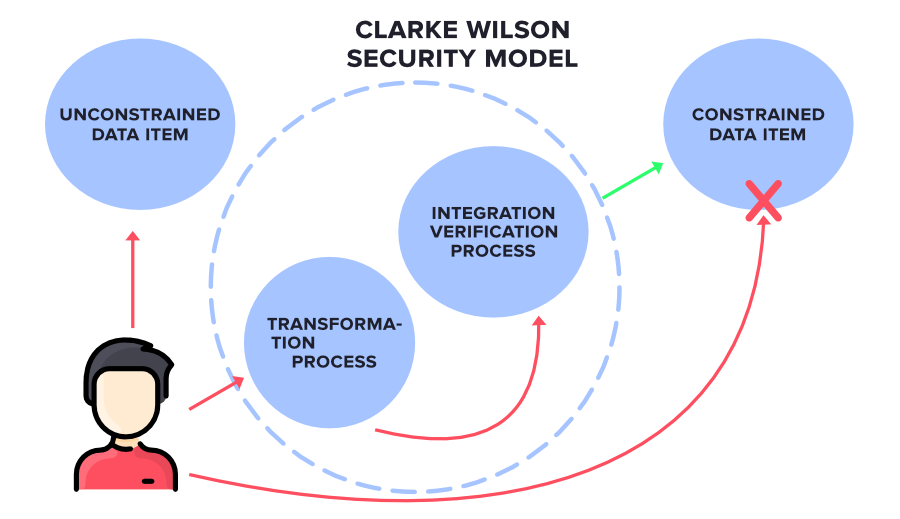
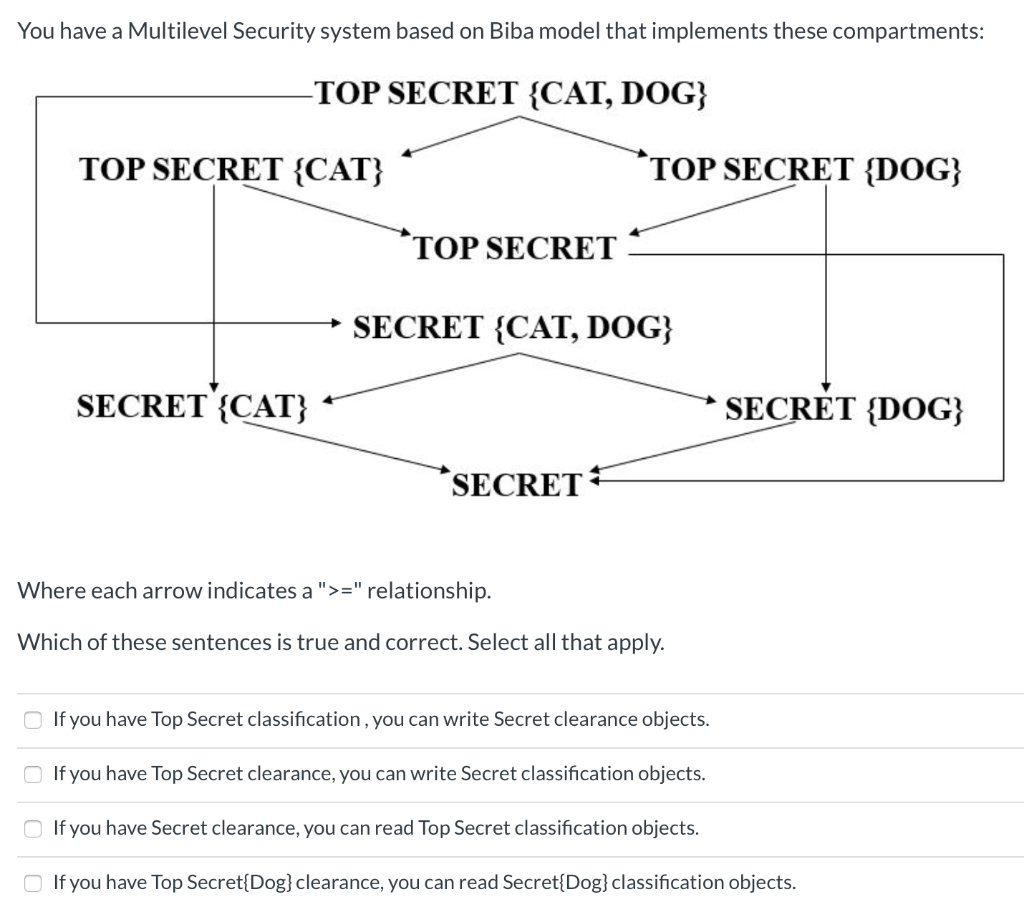
Two Laws of Biba Model The satisfaction of both Biba laws, prevents the... | Download Scientific Diagram

Two Laws of Biba Model The satisfaction of both Biba laws, prevents the... | Download Scientific Diagram

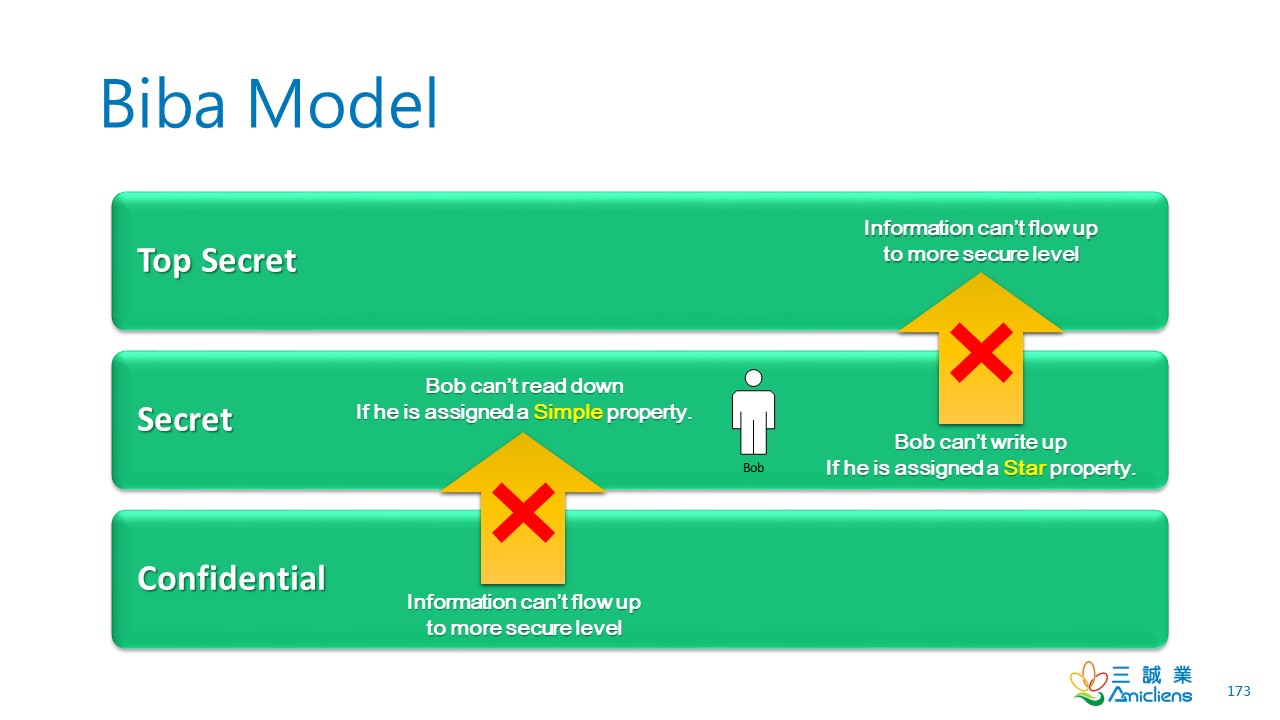
Two Laws of Biba Model The satisfaction of both Biba laws, prevents the... | Download Scientific Diagram

Improved Biba model based on trusted computing - Liu - 2015 - Security and Communication Networks - Wiley Online Library